Security & Encryption
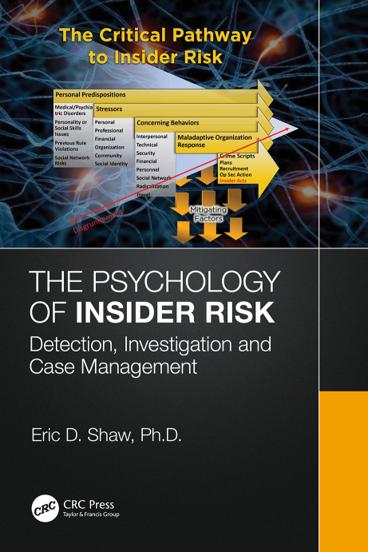
pdf |en | | Author: Eric Shaw
( Category:
Online Safety & Piracy
May 24,2023 )
epub |eng | 2023-04-14 | Author:Richard Coyne [Coyne, Richard]
Figure 9.2 Reconstruction of Albertiâs map of Rome as it appeared in Descriptio urbis Romae, by architect Luigi Vagnetti (1915â1980) in Lo studio di Roma negli scritti albertiani (1974). The ...
( Category:
Cryptography
May 23,2023 )
pdf |en | | Author: Ravindra Das
( Category:
Encryption
May 18,2023 )
epub, pdf |eng | 2020-02-21 | Author:Shashi Shekhar & Pamela Vold [Shekhar, Shashi & Vold, Pamela]
Figure 11 City of Minneapolis. Source: Minnesota Spatial Computing Group. Limitations and Concerns Because GIS is a visualization tool, it can also be used to represent data inaccurately. For example, ...
( Category:
Privacy & Online Safety
May 13,2023 )
pdf | | 2002-09-21 | Author:Flavio Bernardotti
( Category:
Viruses
May 6,2023 )
epub |eng | 2023-04-20 | Author:J. Morris Chang, Di Zhuang, Dumindu Samaraweera [J. Morris Chang, Di Zhuang, Dumindu Samaraweera]
Figure 6.1 The synthetic data retains the structure of the original data, but they are not the same. Synthetic data can also be utilized in business scenarios. For instance, suppose ...
( Category:
Privacy & Online Safety
May 4,2023 )
epub |eng | | Author:Unknown
10.6 The âFURNITUREâ AR-AI Application 10.6.1 The Concept of the Application During the research work concerning the fusion of AR and AI technologies, an intelligent mobile application was designed having ...
( Category:
Cryptography
May 2,2023 )
pdf | | 2004-07-29 | Author:Peter H. Gregory
( Category:
Viruses & Malware
April 28,2023 )
pdf | | 2009-03-05 | Author:Unknown
( Category:
Privacy & Online Safety
April 27,2023 )
pdf | | 2008-10-31 | Author:Unknown
( Category:
Privacy & Online Safety
April 27,2023 )
epub |eng | 2020-03-29 | Author:SJ Grey [Grey, SJ]
Chapter Twenty-Eight âWell?â asked Geoff, standing in the motion-activated spotlight on the front doorstep. âWhich part of youâre not welcome here are you struggling with?â His grip was steady on ...
( Category:
Online Safety & Piracy
April 20,2023 )
pdf |en | | Author: coll.
( Category:
Cryptography
April 13,2023 )
pdf | | 2012-11-15 | Author:Barnett, Ryan(Author)
( Category:
Online Safety & Piracy
April 13,2023 )
pdf | | 0101-01-01 | Author:Zamzar
( Category:
Viruses
April 6,2023 )
epub |eng | 2014-07-03 | Author:unknow
8 Getting to the Dark Side of the Moon Researching the Lives of Women in Cartography Will C. van den Hoonaard Little did I suspect that a research project conceived ...
( Category:
Encryption
April 3,2023 )
Categories
| Cryptography | Encryption |
| Hacking | Network Security |
| Privacy & Online Safety | Security Certifications |
| Viruses |
Popular ebooks
Practical Threat Detection Engineering by Megan Roddie & Jason Deyalsingh & Gary J. Katz(7660)Effective Threat Investigation for SOC Analysts by Yahia Mostafa;(7485)
Practical Memory Forensics by Svetlana Ostrovskaya & Oleg Skulkin(7204)
Machine Learning Security Principles by John Paul Mueller(7158)
Attacking and Exploiting Modern Web Applications by Simone Onofri & Donato Onofri(6830)
Operationalizing Threat Intelligence by Kyle Wilhoit & Joseph Opacki(6796)
Solidity Programming Essentials by Ritesh Modi(4586)
Microsoft 365 Security, Compliance, and Identity Administration by Peter Rising(4179)
Operationalizing Threat Intelligence by Joseph Opacki Kyle Wilhoit(3927)
Building a Next-Gen SOC with IBM QRadar: Accelerate your security operations and detect cyber threats effectively by Ashish M Kothekar(3678)
Learn Computer Forensics - Second Edition by William Oettinger(3678)
Future Crimes by Marc Goodman(3592)
Blockchain Basics by Daniel Drescher(3574)
Mastering Azure Security by Mustafa Toroman and Tom Janetscheck(3542)
Mastering Python for Networking and Security by José Manuel Ortega(3494)
Incident Response with Threat Intelligence by Roberto Martínez(3409)
The Code Book by Simon Singh(3179)
Mastering Bitcoin: Programming the Open Blockchain by Andreas M. Antonopoulos(3035)
Mobile App Reverse Engineering by Abhinav Mishra(2998)
From CIA to APT: An Introduction to Cyber Security by Edward G. Amoroso & Matthew E. Amoroso(2913)